I took my go-to cookie dough recipe and perfected it to make 3 of my very favorite cookies: Chewy Chocolate Chunk, White Chocolate Chip Macadamia, and Triple Chocolate Chip Chocolate Cookies!
This helper function gives you friendlier syntax to set browser cookies. Refer to the Input Library for a description of its use, as this function is an alias for CIInput::setcookie. Round Cookie Cans Size 1 - 6-11/16' dia. Size 2 - 7-3/16' dia. Size 3 - 8-1/8' or 7-7/8' dia. Size 5 - 9-7/8' dia. Size 115 - 9-7/8' dia. Upright Round Cans Quart & 1/2 Quart 1/2 Gallon.
My recipe is a little different however. If you want your dough to be perfect you MUST use real butter and make sure it is unsalted. I use Land O Lakes. Of cream cheese, not 3oz. 1 1/2 cup sugar, 1 cup of unsalted butter, 1 8oz cream cheese, 1 egg, 1 tsp vanilla, 1/2 tsp almond extract, 3 1/2 cup flour and 1 tsp baking powder. ASP.NET Core 3.1 - Cookie Consent. Ken Haggerty Created - Updated 21:49 This article will demonstrate the implementation of ASP.NET Core GDPR Consent features. Once we get the 'cookies' string, is there a clean way to obtain a specific cookie value? It feels a bit clunky to have to parse the string to extract the actual cookie value. I assume there's probably be a helper method in.Net to handle it, but most of my researches circle back to CookieContainer which we can't use when reusing our HttpClient.
Starting the week off in the best way possible. With a massive post all about cookies. Discussing 3 oh so different cookies that have a common denominator – one amazing cookie dough recipe.
I set out to perfect one of our family chocolate chip cookie recipes that pretty much everyone makes over and over again and knows by heart. It actually happens to be one of the first recipes I ever posted on the blog. Over the years I have stumbled upon and created many cookie recipes (all of which I love, of course). But since this recipe is so special to us and is usually only used for chocolate chip cookies, I really wanted to show its versatility by using it as a base recipe to make the cookies you see here.
So technically, our cookie dough recipe can be transformed into 4 different scrumptious cookies. Mind blown. I always knew there was a reason why we all love it so much.
I also want to mention that the base recipe is absolutely lovely and makes the most amazing chocolate chip cookies. But I do always end up tweaking the recipe ingredients a bit just because of the things I’ve learned and tried over the years. The original post can be found HERE. You don’t have to change a thing, but I’m going to be honest and let you know that my updated version of an old classic always gets the most compliments. No matter which recipe you go for, you can’t go wrong though.
Without further ado, let’s jump right in and let me tell you exactly what I did.
One of the most important things to me when it comes to cookies is chewiness. I live for super chewy cookies and am not a big fan of crunchy ones. There’s definitely a time and place for crispy cookies and a tall glass of milk, but 9 out of 10 times I am all about soft, chewy, and tender cookies.
The first change I made was in the flour department. Since bread flour has a higher gluten content than all-purpose flour, it really helps with developing chewiness. I opted to go half and half and I’ve seen the best and noticeable change when using that ratio.
I also decided to use more brown than granulated sugar. Since molasses is added to white sugar to create brown sugar, it not only adds flavor but also extra moisture, which helps with extra chewiness.
Last but not least, I only used unsalted butter in the recipes. The original recipe calls for a combination of butter and shortening, but I rarely have shortening on hand. It’s one of those ingredients I almost never buy and opted to go for all butter out of necessity. In addition to that, I decided to melt the butter and am pretty sure I’ll never go back. Out of all the changes I made, I believe that melting the butter was the most important one in achieving ultra chewy cookies. There’s something about the ratio of melted butter, dry ingredients, and the addition of a good amount of chocolate chunks/chips that can’t be beat.
You’ll notice that while each recipe is very similar, they’re all a little bit different. I told you in the beginning of the post that I tried to perfect the recipe/recipes and I was not kidding. Every single one has been tweaked, taste-tested, and made multiple times to ensure the perfect outcome every time.
The Triple Chocolate Chip Chocolate Cookie recipe has been changed the most and took the longest time to get just right. But I couldn’t be more excited about it. They’re so good!
My hope is that you’ll find this post most helpful and love having every cookie recipe you could need in one spot. I know I will be pulling up this post time and time again to make them since it will take some time till I memorize every change to every recipe. I am sure it won’t be too long before I have it all down though. A day doesn’t go by that we don’t have a cookie in our cookie jar ♥️.
Hope you enjoy these recipes!

- 2 sticks (1 cup) unsalted butter, melted
- 1 1/2 cups light brown sugar
- 1/2 cup granulated sugar
- 3 large eggs
- 2 teaspoons vanilla extract
- 1 teaspoon salt
- 1/2 teaspoon baking soda
- 1/2 teaspoon baking powder
- 1 1/2 cups all-purpose flour
- 1 1/2 cups bread flour
- 1 1/2 cups chocolate chunks
- Preheat your oven to 350 degrees F. Line a baking sheet with parchment paper.
- 1.In the bowl of your stand mixer, combine melted butter, sugars, eggs and vanilla. Mix until smooth, about 2-3 minutes. Add salt, baking soda, and baking powder. Mix another minute or until incorporated.
- 2.With your mixer set to its slowest setting, add 1 1/2 cups all-purpose flour. Mix until combined with the wet mixture. Add the remaining 1 1/2 cups of bread flour and stir until incorporated. Remove bowl from the mixer and using a spatula, add chocolate chunks.
- 3.Using a large cookie scoop, place cookie dough balls onto the prepared baking sheet and put in the oven. Bake for 14-16 minutes or until the edges start to brown and cookies appear to be set. Let cool for a couple of minutes before transferring to wire racks to cool completely. Repeat with remaining cookie dough.
- 2 sticks (1 cup) unsalted butter, melted
- 1 cup light brown sugar
- 1 cup granulated sugar
- 3 large eggs
- 2 teaspoons vanilla extract
- 1 teaspoon salt
- 1/2 teaspoon baking soda
- 1/2 teaspoon baking powder
- 1 1/2 cups all-purpose flour
- 1 1/2 cups bread flour
- 1 cup white chocolate chips
- 1/2 cup unsalted macadamia nuts, roughly chopped
- Preheat your oven to 350 degrees F. Line a baking sheet with parchment paper.
- 2.In the bowl of your stand mixer, combine melted butter, sugars, eggs & egg yolk and vanilla. Mix until smooth, about 2-3 minutes. Add salt, baking soda, and baking powder. Mix another minute or until incorporated.
- 3.With your mixer set to its slowest setting, add 1 1/2 cups all-purpose flour. Mix until combined with the wet mixture. Add the remaining 1 1/2 cups of bread flour and stir until incorporated. Remove bowl from the mixer and using a spatula, add white chocolate chips and macadamia nuts.
- 4.Using a large cookie scoop, place cookie dough balls onto the prepared baking sheet and put in the oven. Bake for 14-16 minutes or until the edges start to brown and cookies appear to be set. Let cool for a couple of minutes before transferring to wire racks to cool completely. Repeat with remaining cookie dough.
- 1/2 cup (1 stick) unsalted butter
- 4 ounces dark chocolate, roughly chopped
- 1 cup light brown sugar
- 1/2 cup granulated sugar
- 2 large eggs
- 1 teaspoon vanilla extract
- 1/2 teaspoon salt
- 1/2 teaspoon baking soda
- 1 cup all-purpose flour
- 1/2 unsweetened cocoa powder
- Preheat oven to 325 degrees F. Line a baking sheet with parchment paper.
- 1. In a heatproof bowl, combine butter and chopped dark chocolate. Place in the microwave and heat in 30 second intervals until completely melted. Pour mixture into the bowl of your stand mixer and let cool for 2-3 minutes.
- 2. Add sugars and mix until combined. Add eggs and vanilla and cream together. Next, mix in salt and baking soda until incorporated. Add flour and cocoa powder and mix until fully combined. Remove bowl from the mixer and fold in white chocolate chips, milk chocolate chips and semisweet chocolate chips.
- 3. Using a regular cookie scoop, place cookie dough balls onto prepared baking sheet and put in the oven. Bake cookies for 14 minutes. Let cool on the baking sheet for 5 minutes before transferring to wire racks to cool completely. Repeat with remaining dough.
Related posts:
By Rick Anderson
ASP.NET Core Identity is a complete, full-featured authentication provider for creating and maintaining logins. However, a cookie-based authentication provider without ASP.NET Core Identity can be used. For more information, see Introduction to Identity on ASP.NET Core.
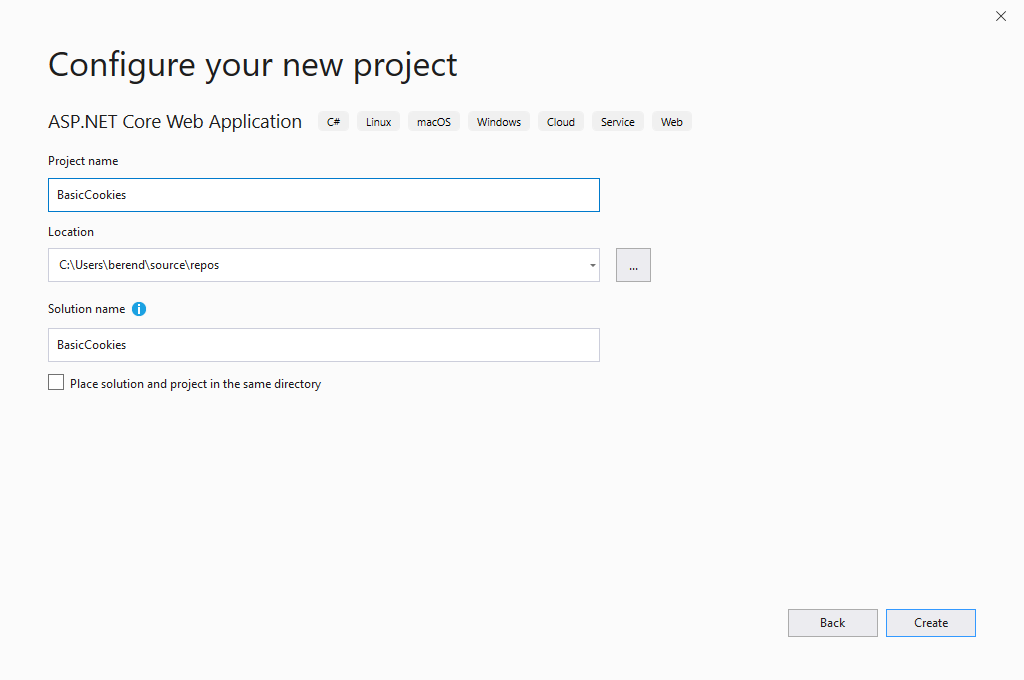
View or download sample code (how to download)
For demonstration purposes in the sample app, the user account for the hypothetical user, Maria Rodriguez, is hardcoded into the app. Use the Email address maria.rodriguez@contoso.com and any password to sign in the user. The user is authenticated in the AuthenticateUser method in the Pages/Account/Login.cshtml.cs file. In a real-world example, the user would be authenticated against a database.
Configuration
In the Startup.ConfigureServices method, create the Authentication Middleware services with the AddAuthentication and AddCookie methods:
AuthenticationScheme passed to AddAuthentication sets the default authentication scheme for the app. AuthenticationScheme is useful when there are multiple instances of cookie authentication and you want to authorize with a specific scheme. Setting the AuthenticationScheme to CookieAuthenticationDefaults.AuthenticationScheme provides a value of 'Cookies' for the scheme. You can supply any string value that distinguishes the scheme.
The app's authentication scheme is different from the app's cookie authentication scheme. When a cookie authentication scheme isn't provided to AddCookie, it uses CookieAuthenticationDefaults.AuthenticationScheme ('Cookies').
The authentication cookie's IsEssential property is set to true by default. Authentication cookies are allowed when a site visitor hasn't consented to data collection. For more information, see General Data Protection Regulation (GDPR) support in ASP.NET Core.
In Startup.Configure, call UseAuthentication and UseAuthorization to set the HttpContext.User property and run Authorization Middleware for requests. Call the UseAuthentication and UseAuthorization methods before calling UseEndpoints:
The CookieAuthenticationOptions class is used to configure the authentication provider options.

Set CookieAuthenticationOptions in the service configuration for authentication in the Startup.ConfigureServices method:
Cookie Policy Middleware
Cookie Policy Middleware enables cookie policy capabilities. Adding the middleware to the app processing pipeline is order sensitive—it only affects downstream components registered in the pipeline.
Use CookiePolicyOptions provided to the Cookie Policy Middleware to control global characteristics of cookie processing and hook into cookie processing handlers when cookies are appended or deleted.
The default MinimumSameSitePolicy value is SameSiteMode.Lax to permit OAuth2 authentication. To strictly enforce a same-site policy of SameSiteMode.Strict, set the MinimumSameSitePolicy. Although this setting breaks OAuth2 and other cross-origin authentication schemes, it elevates the level of cookie security for other types of apps that don't rely on cross-origin request processing.
The Cookie Policy Middleware setting for MinimumSameSitePolicy can affect the setting of Cookie.SameSite in CookieAuthenticationOptions settings according to the matrix below.
| MinimumSameSitePolicy | Cookie.SameSite | Resultant Cookie.SameSite setting |
|---|---|---|
| SameSiteMode.None | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict |
| SameSiteMode.Lax | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.Lax SameSiteMode.Lax SameSiteMode.Strict |
| SameSiteMode.Strict | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.Strict SameSiteMode.Strict SameSiteMode.Strict |
Create an authentication cookie
To create a cookie holding user information, construct a ClaimsPrincipal. The user information is serialized and stored in the cookie.
Create a ClaimsIdentity with any required Claims and call SignInAsync to sign in the user:
If you would like to see code comments translated to languages other than English, let us know in this GitHub discussion issue.
SignInAsync creates an encrypted cookie and adds it to the current response. If AuthenticationScheme isn't specified, the default scheme is used.
RedirectUri is only used on a few specific paths by default, for example, the login path and logout paths. For more information see the CookieAuthenticationHandler source.
ASP.NET Core's Data Protection system is used for encryption. For an app hosted on multiple machines, load balancing across apps, or using a web farm, configure data protection to use the same key ring and app identifier.
Sign out
To sign out the current user and delete their cookie, call SignOutAsync:
If CookieAuthenticationDefaults.AuthenticationScheme (or 'Cookies') isn't used as the scheme (for example, 'ContosoCookie'), supply the scheme used when configuring the authentication provider. Otherwise, the default scheme is used.
When the browser closes it automatically deletes session based cookies (non-persistent cookies), but no cookies are cleared when an individual tab is closed. The server is not notified of tab or browser close events.
React to back-end changes
Once a cookie is created, the cookie is the single source of identity. If a user account is disabled in back-end systems:
- The app's cookie authentication system continues to process requests based on the authentication cookie.
- The user remains signed into the app as long as the authentication cookie is valid.
The ValidatePrincipal event can be used to intercept and override validation of the cookie identity. Validating the cookie on every request mitigates the risk of revoked users accessing the app.
One approach to cookie validation is based on keeping track of when the user database changes. If the database hasn't been changed since the user's cookie was issued, there's no need to re-authenticate the user if their cookie is still valid. In the sample app, the database is implemented in IUserRepository and stores a LastChanged value. When a user is updated in the database, the LastChanged value is set to the current time.
In order to invalidate a cookie when the database changes based on the LastChanged value, create the cookie with a LastChanged claim containing the current LastChanged value from the database:
To implement an override for the ValidatePrincipal event, write a method with the following signature in a class that derives from CookieAuthenticationEvents:
The following is an example implementation of CookieAuthenticationEvents:
Register the events instance during cookie service registration in the Startup.ConfigureServices method. Provide a scoped service registration for your CustomCookieAuthenticationEvents class:
Consider a situation in which the user's name is updated—a decision that doesn't affect security in any way. If you want to non-destructively update the user principal, call context.ReplacePrincipal and set the context.ShouldRenew property to true.
Warning
The approach described here is triggered on every request. Validating authentication cookies for all users on every request can result in a large performance penalty for the app.
Persistent cookies
You may want the cookie to persist across browser sessions. This persistence should only be enabled with explicit user consent with a 'Remember Me' check box on sign in or a similar mechanism.
The following code snippet creates an identity and corresponding cookie that survives through browser closures. Any sliding expiration settings previously configured are honored. If the cookie expires while the browser is closed, the browser clears the cookie once it's restarted.
Set IsPersistent to true in AuthenticationProperties:
Absolute cookie expiration
An absolute expiration time can be set with ExpiresUtc. To create a persistent cookie, IsPersistent must also be set. Otherwise, the cookie is created with a session-based lifetime and could expire either before or after the authentication ticket that it holds. When ExpiresUtc is set, it overrides the value of the ExpireTimeSpan option of CookieAuthenticationOptions, if set.
The following code snippet creates an identity and corresponding cookie that lasts for 20 minutes. This ignores any sliding expiration settings previously configured.
ASP.NET Core Identity is a complete, full-featured authentication provider for creating and maintaining logins. However, a cookie-based authentication provider without ASP.NET Core Identity can be used. For more information, see Introduction to Identity on ASP.NET Core.
View or download sample code (how to download)
For demonstration purposes in the sample app, the user account for the hypothetical user, Maria Rodriguez, is hardcoded into the app. Use the Email address maria.rodriguez@contoso.com and any password to sign in the user. The user is authenticated in the AuthenticateUser method in the Pages/Account/Login.cshtml.cs file. In a real-world example, the user would be authenticated against a database.
Configuration
If the app doesn't use the Microsoft.AspNetCore.App metapackage, create a package reference in the project file for the Microsoft.AspNetCore.Authentication.Cookies package.
In the Startup.ConfigureServices method, create the Authentication Middleware service with the AddAuthentication and AddCookie methods:
AuthenticationScheme passed to AddAuthentication sets the default authentication scheme for the app. AuthenticationScheme is useful when there are multiple instances of cookie authentication and you want to authorize with a specific scheme. Setting the AuthenticationScheme to CookieAuthenticationDefaults.AuthenticationScheme provides a value of 'Cookies' for the scheme. You can supply any string value that distinguishes the scheme.
The app's authentication scheme is different from the app's cookie authentication scheme. When a cookie authentication scheme isn't provided to AddCookie, it uses CookieAuthenticationDefaults.AuthenticationScheme ('Cookies').
The authentication cookie's IsEssential property is set to true by default. Authentication cookies are allowed when a site visitor hasn't consented to data collection. For more information, see General Data Protection Regulation (GDPR) support in ASP.NET Core.
In the Startup.Configure method, call the UseAuthentication method to invoke the Authentication Middleware that sets the HttpContext.User property. Call the UseAuthentication method before calling UseMvcWithDefaultRoute or UseMvc:

The CookieAuthenticationOptions class is used to configure the authentication provider options.
Set CookieAuthenticationOptions in the service configuration for authentication in the Startup.ConfigureServices method:
Cookie Policy Middleware
Cookie Policy Middleware enables cookie policy capabilities. Adding the middleware to the app processing pipeline is order sensitive—it only affects downstream components registered in the pipeline.
Use CookiePolicyOptions provided to the Cookie Policy Middleware to control global characteristics of cookie processing and hook into cookie processing handlers when cookies are appended or deleted.
The default MinimumSameSitePolicy value is SameSiteMode.Lax to permit OAuth2 authentication. To strictly enforce a same-site policy of SameSiteMode.Strict, set the MinimumSameSitePolicy. Although this setting breaks OAuth2 and other cross-origin authentication schemes, it elevates the level of cookie security for other types of apps that don't rely on cross-origin request processing.
The Cookie Policy Middleware setting for MinimumSameSitePolicy can affect the setting of Cookie.SameSite in CookieAuthenticationOptions settings according to the matrix below.
| MinimumSameSitePolicy | Cookie.SameSite | Resultant Cookie.SameSite setting |
|---|---|---|
| SameSiteMode.None | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict |
| SameSiteMode.Lax | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.Lax SameSiteMode.Lax SameSiteMode.Strict |
| SameSiteMode.Strict | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.Strict SameSiteMode.Strict SameSiteMode.Strict |
Create an authentication cookie
To create a cookie holding user information, construct a ClaimsPrincipal. The user information is serialized and stored in the cookie.
Create a ClaimsIdentity with any required Claims and call SignInAsync to sign in the user:
SignInAsync creates an encrypted cookie and adds it to the current response. If AuthenticationScheme isn't specified, the default scheme is used.
ASP.NET Core's Data Protection system is used for encryption. For an app hosted on multiple machines, load balancing across apps, or using a web farm, configure data protection to use the same key ring and app identifier.
Sign out
To sign out the current user and delete their cookie, call SignOutAsync:
If CookieAuthenticationDefaults.AuthenticationScheme (or 'Cookies') isn't used as the scheme (for example, 'ContosoCookie'), supply the scheme used when configuring the authentication provider. Otherwise, the default scheme is used.
React to back-end changes
Once a cookie is created, the cookie is the single source of identity. If a user account is disabled in back-end systems:
- The app's cookie authentication system continues to process requests based on the authentication cookie.
- The user remains signed into the app as long as the authentication cookie is valid.
The ValidatePrincipal event can be used to intercept and override validation of the cookie identity. Validating the cookie on every request mitigates the risk of revoked users accessing the app.
One approach to cookie validation is based on keeping track of when the user database changes. If the database hasn't been changed since the user's cookie was issued, there's no need to re-authenticate the user if their cookie is still valid. In the sample app, the database is implemented in IUserRepository and stores a LastChanged value. When a user is updated in the database, the LastChanged value is set to the current time.
In order to invalidate a cookie when the database changes based on the LastChanged value, create the cookie with a LastChanged claim containing the current LastChanged value from the database:
To implement an override for the ValidatePrincipal event, write a method with the following signature in a class that derives from CookieAuthenticationEvents:
The following is an example implementation of CookieAuthenticationEvents:
Register the events instance during cookie service registration in the Startup.ConfigureServices method. Provide a scoped service registration for your CustomCookieAuthenticationEvents class:
Consider a situation in which the user's name is updated—a decision that doesn't affect security in any way. If you want to non-destructively update the user principal, call context.ReplacePrincipal and set the context.ShouldRenew property to true.
Celebrity-famed Cookie Chef Launches Delivery Truck In Seattle
Warning
The approach described here is triggered on every request. Validating authentication cookies for all users on every request can result in a large performance penalty for the app.
Persistent cookies
You may want the cookie to persist across browser sessions. This persistence should only be enabled with explicit user consent with a 'Remember Me' check box on sign in or a similar mechanism.
The following code snippet creates an identity and corresponding cookie that survives through browser closures. Any sliding expiration settings previously configured are honored. If the cookie expires while the browser is closed, the browser clears the cookie once it's restarted.
Set IsPersistent to true in AuthenticationProperties:
Absolute cookie expiration
You'll Be Storing Your Eggs In The Freezer From Now On
An absolute expiration time can be set with ExpiresUtc. To create a persistent cookie, IsPersistent must also be set. Otherwise, the cookie is created with a session-based lifetime and could expire either before or after the authentication ticket that it holds. When ExpiresUtc is set, it overrides the value of the ExpireTimeSpan option of CookieAuthenticationOptions, if set.
The following code snippet creates an identity and corresponding cookie that lasts for 20 minutes. This ignores any sliding expiration settings previously configured.